Running Custom Code on a Google Home Mini (Part 2)
Posted on Tue 28 July 2020 in Projects • Tagged with Reverse Engineering, Linux, Exploit, Fuzzing
After the work detailed in part 1, altering the content of the NAND Flash of the Google Home Mini with ease is now possible.
Despite this very privileged access, because of Google’s secure boot implementation, running arbitrary code on the CPU of the device isn’t possible using simple and naive methods.
However, as we’ll see, there is still a way.
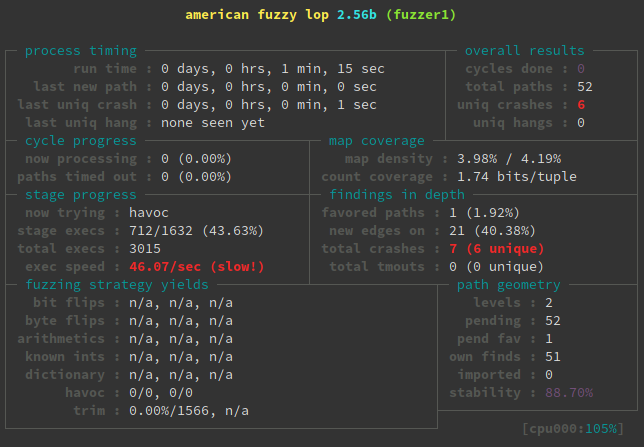
This post will detail how I achieved code execution. It will require fuzzing, understanding some Linux code and finally exploiting a kernel bug.
Of course, NandBug, the hardware tool previously introduced, will be used.
Continue reading
